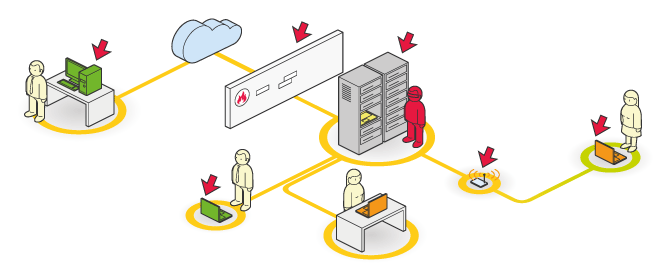
Auditor’ location :
The auditor will be positioned on the internal network and will be able to perform a set of scenarios to test the security of the perimeter held by the mission’s representative.
Targets :
This position primarily allows for the treatment of servers, equipment, or accessible workstations, from the auditor’s location. In most cases, all the technologies accessible to a traditional or wireless network can be treated during this type of mission.
Scenarios:
It is possible to simulate the following penetration scenario :
-
A malicious employee, wishing to perform internal fraud or copy confidential data. In this scenario, depending on the mission representative’s choices, the attacker either has or doesn’t have an account to connect to the mission perimeter.