Risks :
Business applications developed within the company and solutions purchased commercially can contain critical vulnerabilities resulting in risks of piracy or data leaks.
Objectives :
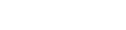
The test d’incursion is designed to identify vulnerabilities present within the application, by simulating the action of a cracker with the aim to penetrate the information system through the diversion of one or more accessible applications.
The penetration test making up the offensive part of the test d’incursion is launched by following two scenarios :
- A user has a password in order to connect to the platform.
- A user does not have a password.
In order to strengthen our offensive capabilities during our application penetration missions, we have capitalised on our skills within one of the first French penetration frameworks, Nemesis.

This technology constitutes the hand tools of the auditor. Nemesis does not allow for the automatic detection of vulnerabilities or the administration of automatic security audit operations.
Maturity :
The mission has been performed at least 20 times with our customers, the procedures were defined, and personnel have been trained in the use of tools and the standardization of the mission.
Remarks :
It is important to note that while this computer penetration mission is being carried out, only an inverse engineering analysis of the first level will be performed. In fact, we will not execute an advanced retro-engineering analysis to decompile and document all of the flaws that may exist within the targeted application.